 Marketing
Marketing
I just received this email… and it made me chuckle….
| From: Eric Johnson <ejohnson@usbfund.com> Subject: * SBA.NET.WEB approved at 3.75% Good morning Wayne! Just wanted to follow-up on our conversation that we had last November 11th, in regards to SBA.NET.WEB’s new projects. We ran a D&B analysis and you scored 76 out of 80 which places you at the top tier in your industry. We still have SBA.NET.WEB approved for a line of credit at 3.75% with access to funds for at least $324,646.00. These funds can be used for unsecured working capital lines of credit or new and used equipment purchases. Call anytime to confirm exact numbers for your funds or simply click here to get a free quote. My Best, Eric Johnson (949) 390-5411 Office “This communication is confidential and may be legally privileged. If you are not the intended recipient, (i) please do not read or disclose to others, (ii) please notify the sender by reply mail, and (iii) please delete this communication from your system. Failure to follow this process may be unlawful. Thank you for your cooperation.” Copyright © 2017 US Business Funding |
 People just don’t get it.
People just don’t get it. 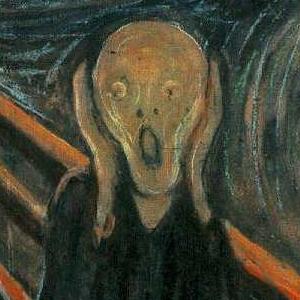
 This is a story of a company that is currently using Excel instead of a real accounting system.
This is a story of a company that is currently using Excel instead of a real accounting system. 
